Identity Protector is an unacceptable computer tool or program that every user wishes to get rid of from their PC. It is deemed an invasive type of software that may be installed on the computer without the user’s full knowledge. This kind of malware is spreading on thousands of computers worldwide through Internet connection. Software exploits and vulnerabilities in Internet browser programs are believed to be exploited by Identity Protector to gain access to the target computer. Malicious links from social media sites and spam email messages also contribute to the delivery of Identity Protector onto the victim’s PC.
How does it infect the computer?
Identity Protector and most rogue applications normally get installed even without the consent of the computer users. In most instances, this rogue tool is downloaded and installed while bundled with various freeware such as media players, utilities, creativity apps, internet speed boosters, VPN apps, or fake software updates. Some call this type of installer “Bloatware” because a number of programs will be installed on the computer with a single setup process. Hence, users have all the chances to exclude whatever is unnecessary if they only care to run the setup in Custom or Advanced mode.
What happens after the installation?
Once Identity Protector is running on the computer, it will begin to display fake warnings and pop-up alerts stating several issues on your computer, especially identity theft concerns. Obviously, these alerts are just a ploy to deceive computer users and force them to pay for the registration.
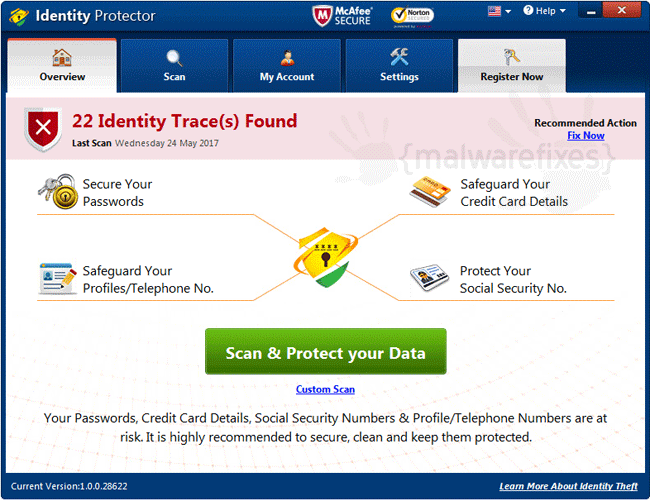
Unlike most rogue applications, Identity Protector will never prompt the user to purchase the full version. Instead, it will issue a registration page where the user needs to input personal data, including credit card details. These details will be used for future billing when using this product or contacting their technical support team.
What to do with the rogue Identity Protector?
As you can see, the Identity Protector program was made to steal money from you using various methods of deception. Never pay for this worthless program and execute the removal steps to eliminate this threat from the computer right away.
Identity Protector Removal Procedure
Below is a systematic instruction that is very useful in getting rid of unwanted programs on compromised Windows computers. Aside from removing the unwanted application, this guide is also helpful for deleting associated adware and malware. In order to totally eliminate the threat, it is vital to follow the process in an exact manner.
Instant Removal : Scan the computer with antivirus program
Combo Cleaner is a trusted computer security and optimization tool equipped with a powerful virus and malware detection engine. This program can get rid of unwanted program Identity Protector and similar threats, whether it has infected PC, Mac, Android, or iOS.
1. Download the application from the following page:
2. Save the file to your preferred location.
3. Double-click the downloaded file CCSetup.exe and install with the default settings.
4. At the end of the setup process, click Finish to run Combo Cleaner.
5. The tool will update the database file; please wait for this process to complete.
6. To begin checking for threats like Identity Protector, click on the Start Scan button. Wait for this scan to finish.

7. At the end of the scan process, click on Remove all threats to delete Identity Protector, including all harmful objects from the computer.
To fully optimize the features of antivirus and privacy scanners, users may have to upgrade to the premium version.
Please continue with the succeeding removal procedures if you are comfortable manually getting rid of the unwanted program and malicious items linked to it.
Manual Removal : Steps to get rid of Identity Protector
The steps below will guide you to manually remove Identity Protector without having to purchase a recommended virus scanner. We have tested the procedures; hence, the attackers may make modifications overtime. As a result, terms, names, and images in the guide may differ from what users are seeing recently.
The procedure may require you to close the browser or restart the computer; therefore, we are suggesting to Bookmark or Print this page. You must be logged in to Windows with an Administrator account to be able to execute some of the tasks. Check here to know if you are currently using an account with Admin rights.Step 1 : Restart Windows in Safe Mode with Networking
The method of running Windows in Safe Mode before deleting files, ending system processes, and virus scanning is effective in getting rid of Identity Protector. This routine can prevent most viruses and malware from loading, making it easier to detect and remove them.
1. On the Windows Search bar, please type msconfig.

2. Select and open System Configutation on the list of found results.
3. Once you are in the System Configuration window, go to the Boot tab.

4. Under the Boot Options area, please check Safe Boot so that it starts in Safe Mode after restarting.
5. Next, select Network. This will allow Windows to boot in Safe Mode with Networking.
6. Lastly, click on Apply and OK to save the changes.
7. Please restart Windows. The system should run in Safe Mode after the reboot.
Do not forget to restore the normal boot process of Windows after this process. Simply repeat the method above, and this time, uncheck the Safe Boot option to run Windows normally.Step 2 : Uninstall Identity Protector from Windows
1. On your keyboard, press Windows Key + R. Type the appwiz.cpl command and click OK.

2. The Program and Features window will open. Arrange the list in a chronological manner, with recently installed applications on top. To do this, click on the 'Installed On' column.
3. Select Identity Protector or a recently installed suspicious entry from the list.
4. Click on Uninstall to remove it from the Windows system. You can close the Program and Features window once this procedure is done.
Step 3 : Delete Malicious Files and Folder
1. Open Windows File Explorer. You can use the keyboard shortcut Windows Key + E.
2. On the top menu, click on View > Show > Hidden Items. This will expose all hidden files associated with Identity Protector.
3. Now, go to the following directory or file location of the malware:
- C:\Program Files (x86)\Identity Protector\
Keep in mind that Identity Protector may use random folder names. So, if the example above is not present, you can look for any suspicious folder name. Arrange the contents of the "Program Files (x86)" folder chronologically by clicking on the Date Modified tab above to see the most recent added suspicious directory.
4. Select all the files in this suspicious directory and click Delete. You can also just delete the whole folder itself. Please close the File Explorer window after this task.

5. Next, on your Desktop, right-click on Recycle Bin and click on Empty Recycle Bin in the list.
6. Please restart Windows in Normal mode. Refer to Step 3 and just uncheck the Safe Boot option.
You can run a virus scan while in Safe Mode. It has been proven that most malware won't load when Windows is booted to Safe Mode, making it easier to remove them.Step 4 : Scan the computer with AdwCleaner
In this section, we will check the computer with AdwCleaner and reset vital sections of the browser program and network settings that may have been affected by the Identity Protector infection.
1. Follow the link below to download the tool called AdwCleaner.
2. When the download has completed, please close all running programs on the computer, especially browsers affected by Identity Protector.
3. Browse the location of the downloaded file and double-click on adwcleaner.exe to start running the tool.
4. If Windows displays a prompt saying, "Do you want to allow this app to make changes to your device?" click Yes to proceed.
5. On the AdwCleaner dashboard, click on Settings.

6. While in the Settings window, please turn On the Reset Chrome Policies, Reset IE Policies, and Reset Winsock.
7. Go back to the Dashboard and click the Scan Now button.

8. AdwCleaner searches the computer for malicious programs, extensions, plug-ins, adware, and any items that may be associated with Identity Protector.
9. Clean or Remove all suspicious and harmful items identified after the thorough scan.
10. AdwCleaner will then prompt an option to run another repair, which will reset Winsock and other settings. Please click the Run Basic Repair button.

11. A message will appear stating that "All processes will be closed..." Please click Continue.

12. After the cleanup procedure, rebooting the computer is required to finalize the removal of Identity Protector as well as other detected threats.
System Compatibility Notice
We ensured that our method to get rid of Identity Protector is compatible with the majority of Microsoft operating systems (Windows 7, Windows Vista, Windows 8, Windows 10, and Windows 11). To prevent complicated steps, the commands used in the instructions are common, useful, and tested. If you encounter any compatibility problems when following this tutorial, please message us or leave your comment below, and we will reply and make the required modifications.

