Topi ransomware is very similar to Reha, Nosu, and Kodc. These malicious software are included in DJVU ransomware family. If you are still not aware on this kind of computer threat, ransomware are the type of virus that cyber criminal are utilizing to encrypt files on target computer. The victims are forced to purchase a decryption tool and private key to be used for decryption of all encrypted files. This can also be considered as the “ransom fee”.
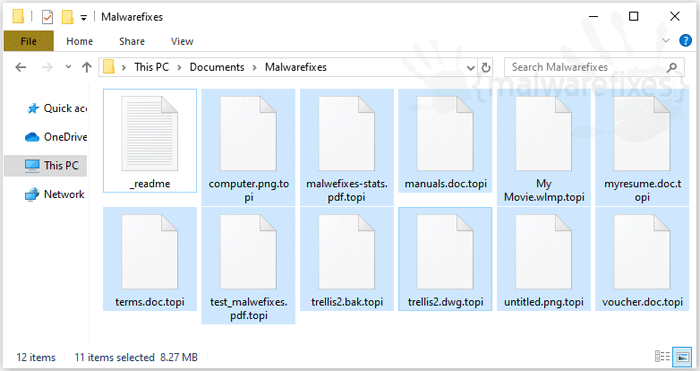
You can recognize an infected file because this ransomware virus will add .topi extension to all encrypted files whether photos, documents, or databases. For example, instead of spreadsheet.xls, it will transform into spreadsheet.xls.topi once encrypted.
Also, Topi developers will notify the victim through a note within the file named _Readme.txt. It contains message stating that majority of files are locked and inaccessible unless a ransom fee is transmitted to attackers. Another thing is, only way to decrypt all infected files is by means of using a decryption tool and private key combination, which is only provided by Topi developers. It is a unique unlocking tool, which can be purchased only from them ranging the price from $490 to $980. Obviously, this is the primary way for Topi developers to generate income. Ransom cost may vary depends on Topi developers and how long the victims will contact the hackers, the sooner, the better. Topi developers offers 50% discount for victims who are able to contact them within the 72 hours period after the initial infection. The victims are instructed to email a copy of personal ID together with one attached file which Topi developers can decrypt free of charge as a way to show that they are capable of restoring the files to its original format.
Unfortunately, not all ransomware developers are complying even their demands are met. For instance, the victim already sent the ransom fee but attackers may still hold back the decryption tool and request for additional payment. Another instance is that, the victim have already settled the ransom money Topi developers are still not sending the tool in exchange, maybe because there isn’t really a tool to deliver.
Topi ransomware is a way to scam and exploit its victims for revenue purposes. If in case you encounter this kind of cyber crime, do not trust the attackers. There is a free way to recover files and that is to restore it from a back up or wait for malware researchers to discover a free tool.
Backup your files
One important step before proceeding with the procedures below is to backup your files. Ransomware attacks are not the same. Each has its own unique set of payloads, aside from encrypting the files with a complex method. Others tend to delete the infected files after a certain period, while others keep them concealed in hidden places. In addition, ransomware decryption tools are not guaranteed to be perfect, and there are instances where files suffer from damages during the decryption process.
So, it is better to create a backup copy of your entire Topi-encrypted files right now.
Topi Ransomware Removal Guide
The first thing to do is remove the Topi virus before attempting the decryption. Remember that as long as the ransomware is active, it will repeatedly encrypt the files on the compromised computer.
Instant Removal : Scan the computer with antivirus program
Combo Cleaner is a trusted computer security and optimization tool equipped with a powerful virus and malware detection engine. This program can get rid of ransomware like Topi through this procedure.
1. Download the application from the following page:
2. Save the file to your preferred location.
3. Double-click the downloaded file CCSetup.exe and install with the default settings.
4. At the end of the setup process, click Finish to run Combo Cleaner.
5. The tool will update the database file; please wait for this process to complete.
6. To begin checking for threats like Topi, click on the Start Scan button. Wait for this scan to finish.

7. At the end of the scan process, click on Remove all threats to delete Topi, including all harmful objects from the computer.
To fully optimize the features of antivirus and privacy scanners, users may have to upgrade to the premium version.
Please continue with the succeeding removal procedures if you are comfortable manually getting rid of the ransomware and malicious items linked to it.
Manual Removal : Steps to get rid of Topi
Infection with the Topi ransomware virus is dangerous to the system because it can inject files that run each time Windows starts. To prevent malicious files from loading, the Windows operating system must run with minimal processes, and this can be done through SafeMode With Networking.
The procedure may require you to close the browser or restart the computer; therefore, we are suggesting to Bookmark or Print this page. You must be logged in to Windows with an Administrator account to be able to execute some of the tasks. Check here to know if you are currently using an account with Admin rights.Step 1 : Start Windows in Safe Mode With Networking
The method of running Windows in Safe Mode before deleting files, ending system processes, and virus scanning is effective in getting rid of Topi. This routine can prevent most viruses and malware from loading, making it easier to detect and remove them.
1. On the Windows Search bar, please type msconfig.

2. Select and open System Configutation on the list of found results.
3. Once you are in the System Configuration window, go to the Boot tab.

4. Under the Boot Options area, please check Safe Boot so that it starts in Safe Mode after restarting.
5. Next, select Network. This will allow Windows to boot in Safe Mode with Networking.
6. Lastly, click on Apply and OK to save the changes.
7. Please restart Windows. The system should run in Safe Mode after the reboot.
Do not forget to restore the normal boot process of Windows after this process. Simply repeat the method above, and this time, uncheck the Safe Boot option to run Windows normally.Step 2 : Scan the Computer with Sophos Home Antivirus
Ransomware files are placed deeply into the system and on various locations, thus, thorough scanning is vital to totally remove Topi virus. Aside from our suggested tool, you may also run your own security program.
To remove Topi ransomware files, scanning the computer with this efficient antivirus tool is suggested. This scanner does not just uncover known threats like viruses or malware, it is also effective in discovering hazardous ransomware like Topi.
1. Please click on the link below to download the program.
2. After downloading, locate the file SophosInstall.exe in the Downloads folder.
3. Install by double-clicking on the file.
4. If it prompts "Do you want to allow this app to make changes on your device?" please click Yes.
5. Next, it will display the Terms and Conditions page. Click the Install button to begin.

6. Run the installation with the default settings. Please note that an internet connection is required in order to download important updates.
7. After finishing the installation, you must login to the dashboard. If you already have a Sophos account, please login. Otherwise, please enter your details and click on the Create Account button.
8. Once you are in the Sophos Home console, click the Scan button to start checking the computer for Topi components.

9. Scanning may take a while; please wait for this process to finish.
10. After scanning the computer, Sophos Home will start cleaning or deleting files infected with Topi.
11. You may now close Sophos Home. The computer is now free from Topi, as well as associated malware and viruses.
The above procedures should have totally eliminated Topi ransomware. However, if you find that there are still remnants of the virus, please proceed to the next steps below.
Step 3 : Double Check with Windows Security Apps
Microsoft Windows has a built-in security application that you can use to double-check if your computer is still infected with Topi. For Windows 10/11 users, please run Windows Security.
Windows 10 / 11 Instructions:
Windows Security is a free tool that was built to help you remove Topi, viruses, and other malicious items from Windows 10/11 systems. Follow these procedures to scan your computer with the tool:
1. Tap or click the Search charm and search for Windows Security
2. Click Open to run the program.

3. On the Dashboard, click Virus and threat protection from the sidebar.

4. On the right panel, click on Scan Options to see different levels of checking the computer.
5. Next, please select Full Scan button.

6. Lastly, click on the Scan now button to start scanning for the presence of Topi. The process may take a while to complete.
7. After the scan, Delete/Quarantine identified threats, whether they were relevant to Topi or not. You may now restart Windows to complete the virus removal process.
For Windows 8.1 and Windows 7, you can scan the computer for free with the Microsoft Malicious Software Removal Tool (MSRT 64-Bit). It is a stand-alone virus scanner tool that targets prevalent malware groups.Recover Files from Topi Ransomware Infection
In this section, we will provide ways to decrypt files infected with Topi ransomware. Aside from dedicated decryption software and common tools, other options for file recovery are provided. As much as we can, we will update this area whenever a new and more suitable decryption tool becomes available.
Find a suitable Topi decryption tool from Emsisoft
This service from Emsisoft is helpful in unlocking encrypted files without paying a ransom. The page provides a list of ransomware decryption tools. All you have to do is look for the specific tool and start recovering the Topi-encrypted file.
How to protect the computer from Topi ransomware?
After the ransomware is removed, it is important to prevent similar incidents from happening again. To effectively protect the computer, the user must know how Topi ransomware was able to infect it. To minimize the possibility of infection, staying away from the common sources of this virus is crucial.
How does ransomware infect your computer?
The method of infecting the computers was found to be similar to that of other common viruses. Ransomware like Topi is seen to have efficient deployment via spam email messages, web injectors, malicious software installers, misleading online advertisements, and Trojan Downloaders.
Once the virus is executed, it immediately infects the system. Then, Topi ransomware communicates with a remote server so that a unique key can be generated for a specific computer. After acquiring the key, it starts to decrypt target files using a complex method that is almost unbreakable. In the final stage of the attack, Topi ransomware demands ransom money in exchange for the decryption tool. To further understand the attack scheme, we have included an infographic below.

What are the essential things to do?
Do a Regular File Back-up - Always backup your data on a separate storage devices such as external hard drives, optical discs, or online backup services.
Keep Your Software Updated - Make sure that you have the latest software updates especially on the operating system. Recent updates often contain vital security patches to help protect the computer against all forms of threats.
Install a Security Program - Protect the computer with effective anti-virus application using efficient real-time scanning. Regularly run a complete scan to check the computer for presence of malware.
Protect your files with Controlled Folder Access (Windows 10/11)
For Windows 10/11 users, aside from protecting the computer using anti-virus or anti-malware programs, one way to protect against ransomware attacks is by using Controlled Folder Access. This feature of Windows Defender Security Center may not prevent the Topi ransomware infection, but it can protect folders and files in general. Follow the steps to enable Controlled Folder Access in Windows 10/11.
1. Go to Windows Search and type Windows Security.

2. Open Windows Security to see all the options.
3. Click Virus and Threat Protection, either on the sidebar or on the main panel.

4. Scroll down to the "Ransomware Protection" area, and click on Manage Ransomware Protection.
5. In the "Controlled Folder Access" section, turn the slider to On. This will enable the feature and protect the folder against Topi virus or any type of ransomware.

6. Click on Protected Folders to see the list of included folders. If Windows displays a message, "Do you want to allow this app to make changes to your device?" please click Yes to proceed.

7. Click on the Add a Protected Folders button to include additional folders. Make sure that folders with important files are included in the list.
Troubleshooting Guide
Certain programs may be blocked by the Controlled Folder Access feature. To fix the issue, simply have the specific program whitelisted.
1. Under the "Controlled Folder Access" section, click Allow an app through Controlled folder access.
2. If Windows displays the message "Do you want to allow this app to make changes to your device?" click Yes to continue.
3. Next, click the Add an allowed app button.

4. Lastly, click on the Recently blocked app and remove the program from the list of blocked applications.
This Controlled Folder Access feature is one way to protect files against Topi ransomware. Other important things to do to keep files safe against ransomware are early prevention, like keeping programs updated, installing an efficient security program, and doing regular file backups on a separate media drive.
System Compatibility Notice
We ensured that our method to get rid of Topi is compatible with the majority of Microsoft operating systems (Windows 7, Windows Vista, Windows 8, Windows 10, and Windows 11). To prevent complicated steps, the commands used in the instructions are common, useful, and tested. If you encounter any compatibility problems when following this tutorial, please message us or leave your comment below, and we will reply and make the required modifications.


Please let me know when Topi extension tool comes.
This is work for 100% right?