The domain Googleapis.com is owned and operated by Google. This is used by several programs and applications to interact with and obtain data from one another. For example, if an application or website is using services from Google like Maps, Emails, Analytics, Cloud, and so on, an API is needed to have better collaboration between the application or website and Google services. With regards to Storage.googleapis.com, it is a subdomain that hosts several services and platforms, including Google Cloud Storage.
Is Storage.googleapis.com harmful?
As stated, Storage.googleapis.com is a subdomain that hosts Google Cloud Storage. This is a file hosting service offering different products that fit the requirements of several online businesses and software developers. The bad thing is, even cyber offenders are taking advantage of Storage.googleapis.com for their online fraudulent activities. They are abusing it to deploy malicious programs, phishing scams, spamming, and many other online counterfeiting activities. This is not a new thing, and the company is very aware of it. Google is taking all the necessary measures to control this abuse. In fact, anyone can report suspected abuse on Google Cloud Platform for any misuse of services that run on Google infrastructure.
Malware detected on Storage.googleapis.com
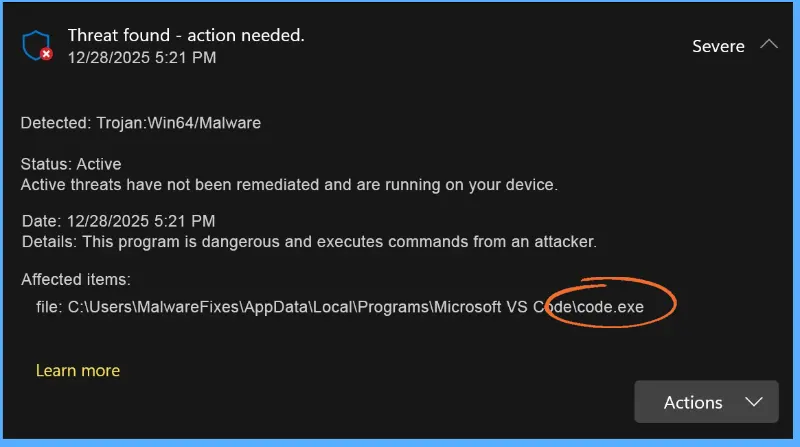
It is possible that your anti-virus or anti-malware program detects harmful activities or objects from Storage.googleapis.com. As stated, there are clients on this server who are abusive. Also, malware that is present on the computer may tend to communicate with the attacker’s server on Storage.googleapis.com. The anti-virus application senses this suspicious behavior, and the tendency is to block the connection in order to avoid any harm. See the sample image below to see how a real-time security program detects and blocks the outbound connection to Storage.googleapis.com.
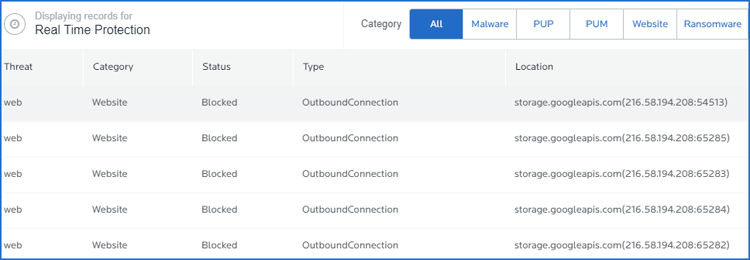
In the event that a computer security application sends an alert about suspicious activities involving Storage.googleapis.com, immediately run a complete scan to detect the culprit. Malware could be present on the computer that triggers the suspicious connection to Storage.googleapis.com.
Threat behavior
Installation
Malware, Trojan, or virus running on the computer may redirect the affected browser to a drive-by-download web site such as Storage.googleapis.com. Attackers are using this method to spread threats using various web addresses to evade the general blocking capability of most security programs. That is why regular updating of your anti-virus and anti-malware programs is vital.
Typically, redirects, hijackers, and other relevant threats are embedded in potentially unwanted programs (PUP) or altered legitimate free software like tools, games, multimedia players, and software updates.
Symptoms
If Storage.googleapis.com starts to download and install unwanted programs on visitor’s computers, there are really no obvious signs except for sluggish system performance. If your computer is equipped with an effective security tool, you might get alerted with a pop-up message stating that your computer is under attack by Storage.googleapis.com.
Browser redirection to Storage.googleapis.com and other strange changes on browsers like Internet Explorer, Google Chrome, and Mozilla Firefox are also signs that Storage.googleapis.com is initiating an assault on your computer.
How to Remove Storage.googleapis.com
To totally remove Storage.googleapis.com from the computer and get rid of relevant viruses and trojans, please execute the procedures as stated on this page. Make sure that you have completely scanned the system with the suggested malware removal tools and virus scanners.
Instant Removal : Scan the computer with antivirus program
Combo Cleaner is a trusted computer security and optimization tool equipped with a powerful virus and malware detection engine. This program can get rid of computer virus like Storage.googleapis.com through this procedure.
1. Download the application from the following page:
2. Save the file to your preferred location.
3. Double-click the downloaded file CCSetup.exe and install with the default settings.
4. At the end of the setup process, click Finish to run Combo Cleaner.
5. The tool will update the database file; please wait for this process to complete.
6. To begin checking for threats like Storage.googleapis.com, click on the Start Scan button. Wait for this scan to finish.

7. At the end of the scan process, click on Remove all threats to delete Storage.googleapis.com, including all harmful objects from the computer.
To fully optimize the features of antivirus and privacy scanners, users may have to upgrade to the premium version.
Please continue with the succeeding removal procedures if you are comfortable manually getting rid of the computer virus and malicious items linked to it.
Manual Removal : Steps to get rid of Storage.googleapis.com
The steps below will guide you to manually remove Storage.googleapis.com without having to purchase a recommended virus scanner. We have tested the procedures; hence, the attackers may make modifications overtime. As a result, terms, names, and images in the guide may differ from what users are seeing recently.
The procedure may require you to close the browser or restart the computer; therefore, we are suggesting to Boookmark or Print this page. You must be logged in to Windows with an Administrator account to be able to execute some of the tasks. Check here to know if you are currently using an account with Administrative rights.Step 1 : Start Windows in Safe Mode With Networking
The method of running Windows in Safe Mode before deleting files, ending system processes, and virus scanning is effective in getting rid of Storage.googleapis.com. This routine can prevent most viruses and malware from loading, making it easier to detect and remove them.
1. On the Windows Search bar, please type msconfig.

2. Select and open System Configutation on the list of found results.
3. Once you are in the System Configuration window, go to the Boot tab.

4. Under the Boot Options area, please check Safe Boot so that it starts in Safe Mode after restarting.
5. Next, select Network. This will allow Windows to boot in Safe Mode with Networking.
6. Lastly, click on Apply and OK to save the changes.
7. Please restart Windows. The system should run in Safe Mode after the reboot.
Do not forget to restore the normal boot process of Windows after this process. Simply repeat the method above, and this time, uncheck the Safe Boot option to run Windows normally.Step 2 : Uninstall Unwanted Application
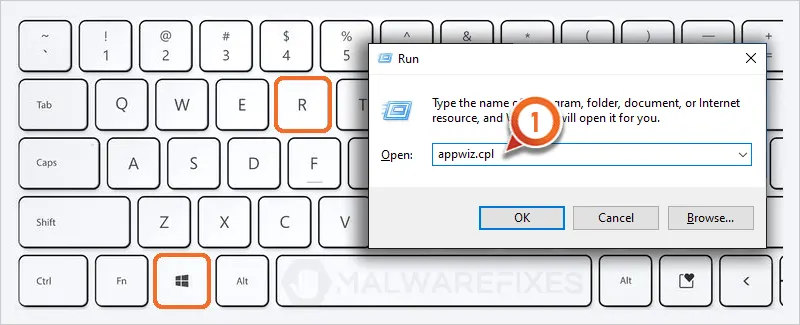
1. Open the Program and Features window by using the keyboard shortcut. Press Windows Key + R and type appwiz.cpl in the dialog box and click OK.
2. Arrange the date in chronological order to see the most recently installed program; click on the Installed On to do this.
3. Now, locate the unwanted program from the list; this may be related to Storage.googleapis.com.
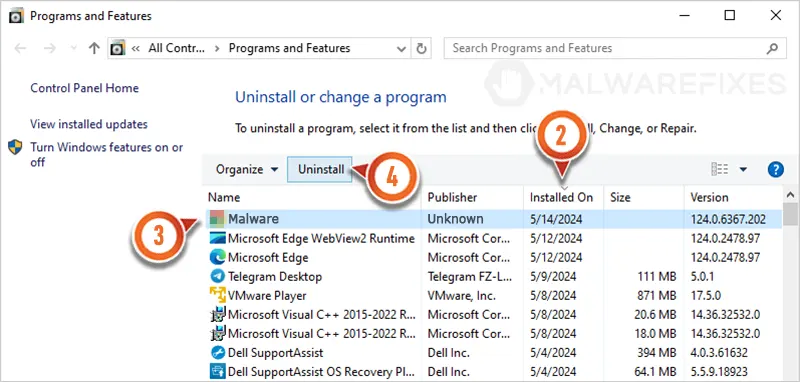
4. Click the Uninstall button to proceed with the removal of the unwanted program.
Step 3 : Show Hidden Files
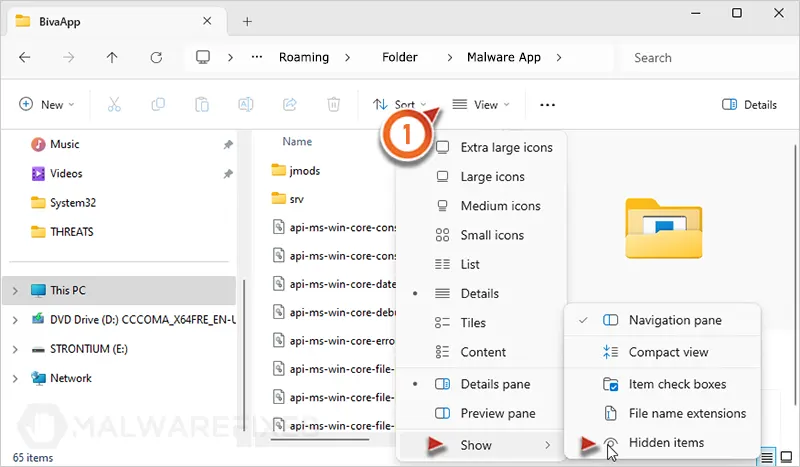
1. Open File Explorer and go to the top menu and click on View, and then select Show, then Hidden Items to reveal hidden files.
Step 4 : End Malware Task
1. On your keyboard, press Ctrl + Alt + Del and click on Task Manager from the selection.
2. Locate the malicious task from the Apps list and right-click on it.
3. Select Open file location.
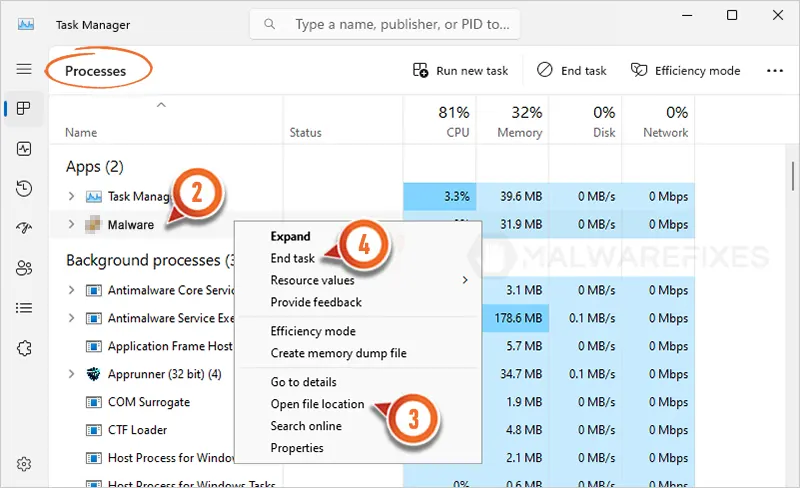
4. Lastly, right-click on the malicious task and select End Task from the options.
Step 5 : Locate and Delete Malicious Files
Once you open the file location, check if it is part of a program. You may uninstall the entire unwanted application by executing the procedures in Step 2. If it is a stand-alone file, you can manually delete it.
Locating and deleting the file detected by an antivirus program is also suggested to completely eliminate Storage.googleapis.com.
Step 6 : Run Sophos Home Virus Scanner
To remove Storage.googleapis.com hidden files, scanning the computer with this powerful virus and malware removal tool is recommended. This scanner does not just uncover known threats like viruses or malware; it is also effective in discovering harmful files associated to Storage.googleapis.com.
1. Please click on the link below to download the program.
2. After downloading, locate the file SophosInstall.exe in the Downloads folder.
3. Install by double-clicking on the file.
4. If it prompts "Do you want to allow this app to make changes on your device?" please click Yes.
5. Next, it will display the Terms and Conditions page. Click the Install button to begin.

6. Run the installation with the default settings. Please note that an internet connection is required in order to download important updates.
7. After finishing the installation, you must login to the dashboard. If you already have a Sophos account, please login. Otherwise, please enter your details and click on the Create Account button.
8. Once you are in the Sophos Home console, click the Scan button to start checking the computer for Storage.googleapis.com components.

9. Scanning may take a while; please wait for this process to finish.
10. After scanning the computer, Sophos Home will start cleaning or deleting files infected with Storage.googleapis.com.
11. You may now close Sophos Home. The computer is now free from Storage.googleapis.com, as well as associated malware and viruses.
After executing the above instructions, Storage.googleapis.com should have been completely removed from the computer. If there are still signs of infection or the computer is displaying unusual behaviors, please continue with the remaining procedures.
Another alternative for Windows 10/11 users is to scan the computer with Microsoft Defender Offline. This will run a virus scan in the recovery environment.Step 7 : Double Check with Windows Security Apps
Microsoft Windows has a built-in security application that you can use to double-check if your computer is still infected with Storage.googleapis.com. For Windows 10/11 users, please run Windows Security.
Windows 10 / 11 Instructions:
Windows Security is a free tool that was built to help you remove Storage.googleapis.com, viruses, and other malicious items from Windows 10/11 systems. Follow these procedures to scan your computer with the tool:
1. Tap or click the Search charm and search for Windows Security
2. Click Open to run the program.

3. On the Dashboard, click Virus and threat protection from the sidebar.

4. On the right panel, click on Scan Options to see different levels of checking the computer.
5. Next, please select Full Scan button.

6. Lastly, click on the Scan now button to start scanning for the presence of Storage.googleapis.com. The process may take a while to complete.
7. After the scan, Delete/Quarantine identified threats, whether they were relevant to Storage.googleapis.com or not. You may now restart Windows to complete the virus removal process.
For Windows 8.1 and Windows 7, you can scan the computer for free with the Microsoft Malicious Software Removal Tool (MSRT 64-Bit). It is a stand-alone virus scanner tool that targets prevalent malware groups.System Compatibility Notice
We ensured that our method to get rid of Storage.googleapis.com is compatible with the majority of Microsoft operating systems (Windows 7, Windows Vista, Windows 8, Windows 10, and Windows 11). To prevent complicated steps, the commands used in the instructions are common, useful, and tested. If you encounter any compatibility problems when following this tutorial, please message us or leave your comment below, and we will reply and make the required modifications.
Originally published on April 21, 2015 at 10:12


@MELISSA HOLYOKE,
Have you tried to login to your online Gmail account and “Block” the sender? To do this, please follow these steps:
1. Login to your online Gmail account.
2. Open the email from google.apeis.com.
3. On upper-right corner of the message, click the Ellipses (3dots).
4. On the drop-down list, click “Block…”
I just add googleapis.com to my users host file and point it to 127.0.0.1.
Any attempt to access that address will fail.
We have also made it a company policy and block all access to google.com as well.
We automatically check and add our host file entries at login using a login script.
If Google will not protect us from people who use their services in a malicious way, then Google leaves us no choice but to block them completely.
So far, NO ONE HAS COMPLAINED. and we have blocked them for over a year.
Problem solved.
No more infections.
P.S. We provide ongoing training to our employees on internet and email best practices, but people do make mistakes on occasion, but this helps to prevent a few anyway.
This link is for Google Platform Storage services from Google. It’s not installing anything onto your computer. People use Google Platform to store videos, files or whatever, and then gives the user a link. The person shares the link so that someone else can access or view the files. It’s Google’s big data center.
Google is responsible for this domain, how come they do not act on this even if you complain….
Followed the above procedures, paid for Malwarebytes software, still getting emails. Any suggestions?
I need help ok so this is what happened a few days ago y received a drop box link in messenger and I (stupidly) open it when the bowser opened it took me to an error screen in the URL of storage.googleapis.com the error is:
This XML.file does not appear to have any style information associated with it. The document tree is:
User project account problemUser project billing account not in good standing
The billing account for project (some numbers i guess is the file code or something ) is disabled in state delinquent
(the file obviously never showed) The person who I received the message with the link posted 2 days later that it was spam due to a virus but I am not so sure so I wanted to know if this is really the malware of storage.googleapis.com or some other malware or if it’s something else please help me I am kind of paranoiac about it I have some work information on that phone
I have downloaded TotalAV but I cannot log in now. Each time I get the message that my password is wrong.
VIRUS STORAGE.GOOGLEAPIS.COM VIRUS IN FACEBOOK
My computer has been blocked.
Error # DW6VB6
The following information is being stolen…
Facebook Login
>Credit Card Details
>Email Account Login
>photos stored on this computer
Please mail me the removal process.
My contact no: +8801915130407
Windows defender will find and remove this malware/virus.
Thank you for that explanation, is there any hazard affecting Linux distributions?
Downloaded and paid for the anti malware, but not removed the files it downloaded. I’m unable to uninstall them and the fixes you are recommending above will not remove these, right?
What’s the point? What if there’s a virus in one of the three software we have to download? Why can’t we just have one software that does all of the functions that the other three do?